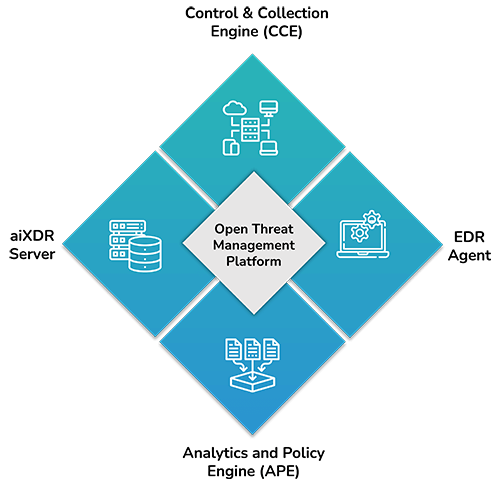
Open Threat Management Platform
CCE | EDR Agent | APE | aiXDR
OTM Platform proactively and confidently raises and eliminates only qualified cybersecurity threats based on available information and knowledge from diverse digital assets, driven by ML-based behavioral analytics and AI-based decision-making.

Drawbacks of Siloed Security Solutions
- Significant redundancy of threats and alerts causing alert fatigue
- Lacks comprehensive datapoints for accurate threat detection
- Operational hassle with disparate dashboards from various tools/ platforms
- High cost of integration, support and maintenance
The Open Threat Management platform was created from the ground up with a 360-degree perspective on cyber security, eliminating the pain, redundancy, and disparities that come with bolt-on siloed solutions. Automation, visibility, insights, and custom controls are all well-balanced in the Open Threat Management Platform. OTM improves analytics, decreases time-to-detection and time-to-remediation, and provides control mechanisms for micro-segmentation and bespoke user-defined-alerts.
Real-time processing at speed
Built-in correlation based on behavioral patterns
Dynamic threat models for attack analysis
OTM Key Components
Control & Collection Engine (CCE)
It orchestrates a collection of events and network traffic data across assets deployed within the enterprise and cloud.
EDR Agent
The lightweight agent resides on each endpoint with the objective of gathering specific information on applications, processes, file events, executables, user access, telemetry etc.
Analytics and Policy Engine (APE)
It forms the core of OTM and processes high-volume high-velocity data in real-time, while feeding threat intelligence, behavioral anomalies, historical context and vulnerability scan results to dynamic threat models driven by actionable AI and ML based correlation.
aiXDR Server
It orchestrates data collection across each tenant, in a multi-tenant environment and relegates specific instructions to the aiXDR agents in communication with the APE.
Get a rapid overview of network traffic across your asset categories and public URLs over time, including data volume, application type, number of bytes, flows, etc.
Dive deeper into threat indicators correlated and analyzed through dynamic threat models, irrespective of the source (network, host, device, ML) and drill down into the actual event with rich contextual data (Event Type, Source, Host, Destination, User Name etc) synthesized in an easy-to-read format.
Define particular auto-remediation criteria based on severity level, confidence level, security warning type, and asset category, including action path (Firewall, NAC, EDR) and schedule, with the least amount of downtime possible.











