Zero Trust Security
Never Trust Always Verify
Address the modern challenges of today’s business and secure infrastructure, remote workers,
hybrid cloud environments, ransomware threats and data for the modern digital transformation.
Zero Trust Security
Never Trust Always Verify
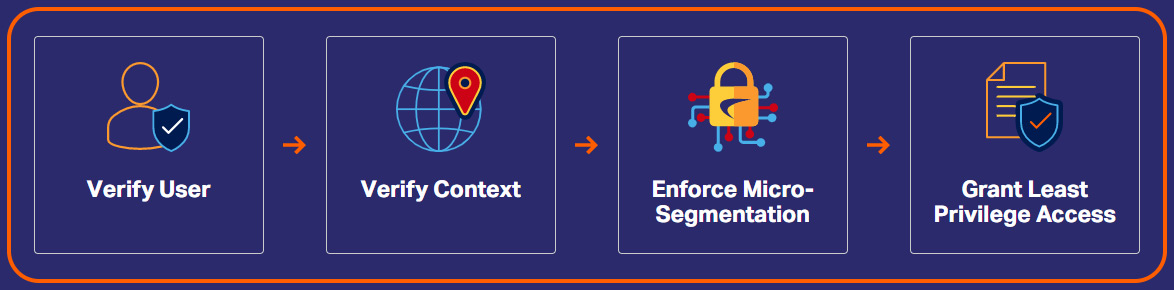
Zero Trust is a strategic cybersecurity approach for current digital corporate settings, which increasingly encompass public and private clouds, SaaS apps, DevOps, robotic process automation (RPA), and other technologies. Zero Trust is based on the idea that businesses should not trust anything automatically, whether it’s outside or inside their network perimeter. Anyone and everything attempting to connect to an organization’s systems must first be verified before access is permitted, according to Zero Trust models. Zero Trust’s major goal is to reduce the danger of cyber assaults in the modernized settings where most businesses operate.
Site Analysis:
We begin with a thorough understanding of the client requirements and environment. Onsite-surveys are done to anticipate the coverage and locations for Wireless access points.
Design High Density & Speed Wireless Solutions:
Once the complete site analysis is over, our team begins with the implementation of high performing wireless solutions that can provide high speed connectivity for users.
Voice, Video & Data:
Our domain experts boast of their ability to deploy multiple advanced applications on wireless networks.

Resources
An organization should treat all of their data, computing services, and devices as resources that need to be protected.

Communication
All communication, both from within and outside the network, must be treated the same and protected in the most secure method available.

Per-Session Access
Each connection to a critical resource or an organization should be established on a per-session basis only.

Dynamic Policy
Access to an organization’s resources should be granted according to the organization’s policy rules and the principle of dynamic least privilege.

Monitoring
To ensure proper data protection and security of corporate resources, organizations should monitor those resources and all actions taken with them.

Continuous Improvement
An organization should gather information about the current state of network assets, infrastructure, and connections to improve the security posture of the network.

Authentication and Authorization
Before granting access to any corporate resource, an organization should enforce dynamic authentication and authorization.
Related Solutions
Security Information & Event Management (SIEM)
Security Information and Event Management (SIEM) provides organizations with next-generation detection, analytics and response.
Network Detection and Response (NDR)
NDR solutions are designed with Machine Learning and Data Analytics to detect cyber-attacks on corporate networks. These continuously analyze..
Extended Detection and Response (aiXDR)
aiXDR protects your borders – remote office, cloud, office, or in transit with the help of razor-sharp analytics, led by Artificial Intelligence & Machine..
Vulnerability Assessment Solutions
Vulnerability Assessment is the process of analyzing vulnerabilities in IT systems. Its goal is to detect the system..
Intrusion Detection System (IDS)
An Intrusion Detection System (IDS) is a system that monitors network traffic for suspicious activity and generate alerts..
User and Entity Behavior Analytics (UEBA)
UEBA is a form of cybersecurity solution or feature that detects threats by looking for such activities that differ from the..
Network Behaviour Anomaly Detection (NBAD)
An integral part Network Behaviour Analysis (NBA), continuously monitoring a propitiatory network to..
SOAR Technology
Cyber-attacks are continually increasing in number and sophistication than ever before. Organizations’ capacity to..
Network Threat Analysis
Network Threat Analysis is a vertical of cybersecurity which monitors the network traffic communications to identify..
Endpoint Detection & Response
Endpoint Detection Response (EDR), also known as Endpoint Detection and Threat Response (EDTR) is an endpoint security..
Advanced SIEM (aiSIEM)
Stop the breach and keep your business running at a low cost. aiSIEM provides round-the-clock protection for your network..
Client Stories

GluCare.Health Enables a Seamless Digital
GluCare.Health Enables a Seamless Digital-First Healthcare Facility in Al Barsha Industry Healthcare Location Dubai, UAE Offerings End-to-End IT Infrastructure Solutions

The H Hotel Enhanced Guest Experience and Operational Excellence through Seamless Network Transformation Industry Consumer & Retail Location Dubai, UAE

Transforming Healthcare: Charisma Medical Centre, UAE Chooses Syscom for IT Infrastructure Industry Consumer & Retail Location Dubai, UAE Offerings Consulting
Insights
Upgrade Your Business WiFi with HPE Networking Instant On
Slow WiFi isn’t just frustrating—it’s costing your business time, productivity, and customer experience. From dropped video calls to lagging

One Network. One Security Strategy. Total Control with Cisco
The New Reality of Business Networks The way businesses operate today has fundamentally changed. Organizations are no longer confined
Power Up Your Wi-Fi Without Powering Up Your Costs
In today’s digital-first world, reliable Wi-Fi is no longer optional-it’s essential. From handling daily operations to supporting multiple connected devices,
Enterprise Digital Transformation
Roadmap
Ready to modernize your business? Our Enterprise Digital Transformation Roadmap provides a strategic, end-to-end approach to migrating and optimizing your IT infrastructure. We guide you through four essential stages to ensure a seamless transition and lasting performance, from Infrastructure Design & Consulting to Deployment & Integration Services.
Infrastructure Design & Consulting
We design tailored IT infrastructure solutions that align with your business goals, ensuring scalability, reliability, and performance.
Project Planning
& Management
From concept to completion, we manage your IT projects with precision, timelines, and transparency to ensure successful delivery.
Technology Procurement
& Optimization
Syscom partners with leading vendors to source, supply, and optimize the right technologies for your specific business needs.
Deployment &
Integration Services
Our experts handle seamless installation and integration of systems — from servers and networks to communication platforms — for smooth operations.
Partner Network

Fortinet
Syscom is a Fortinet Select Integrator and MSSP, delivering advanced, end-to-end cybersecurity solutions to protect, manage, and secure complex modern digital infrastructures.

Cisco
Syscom is an authorized Cisco Select Partner & Provider in the UAE, providing end-to-end IT networking solutions and a wide product range for SMBs and Enterprise-level organizations.

SonicWall
Authorized Platinum Partner of SonicWall in the UAE, providing advanced cybersecurity solutions that deliver robust network protection, threat prevention, and secure connectivity for businesses.

Seceon
Syscom delivers Seceon’s AI-driven cybersecurity solutions, providing real-time threat detection, automated response, and advanced network protection to safeguard businesses from evolving cyber threats.
Palo Alto
Syscom delivers Palo Alto SASE solutions, combining cloud-native security and intelligent networking to provide secure remote access, advanced threat prevention, and seamless performance for modern distributed workplaces.

Sophos
Syscom provides Sophos cybersecurity solutions, delivering advanced threat protection, endpoint security, and secure network management to safeguard businesses and ensure data privacy across all devices and environments.

Barracuda
Syscom is an authorized partner of Barracuda Networks, a leading provider of network security solutions. Barracuda offers innovative, easy-to-deploy, and user-friendly products covering email protection, application and cloud security, network security, and data protection—delivering comprehensive and affordable solutions for businesses.

Forcepoint
Syscom has partnered with Forcepoint as an authorized partner to deliver comprehensive security solutions across the region. We provide access to Forcepoint’s broad portfolio, including cloud-native platforms, data security, and network security solutions.

Securden
Syscom is an authorized distributor of Securden in Dubai, UAE. Securden delivers complete privileged access control, seamless visibility, and advanced access governance across cloud, physical, and virtual environments.

TrendMicro
Trend Micro is a global cybersecurity leader delivering advanced threat protection across cloud, endpoints, networks, and hybrid environments. Its solutions help organizations proactively secure data, stop threats faster, and manage risk with confidence in an evolving digital landscape.

Xcitium
Xcitium is a cybersecurity innovator known for its Zero Trust and container-based protection approach. Its solutions prevent malware execution, secure endpoints and networks, and protect organizations from both known and unknown cyber threats.

Tenable
Tenable is a global leader in exposure management and vulnerability assessment. Its solutions help organizations identify, prioritize, and reduce cyber risks across IT, cloud, and OT environments.

Apphaz
Apphaz is a cybersecurity solutions provider focused on protecting applications and digital assets. Its offerings help organizations identify vulnerabilities, enhance application security, and defend against evolving cyber threats across modern IT environments.

Cydef
Cydef is a cybersecurity company specializing in threat intelligence and cyber risk management. Its solutions help organizations detect threats early, strengthen defenses, and respond effectively to evolving cyber risks.

InstaSafe
Instasafe is a cybersecurity solutions provider focused on zero trust and identity-centric security. Its technologies help organizations secure access, protect users and devices, and enable safe digital operations across modern, distributed environments.











